-
AnyStream is having some DRM issues currently, Netflix is not available in HD for the time being.
Situations like this will always happen with AnyStream: streaming providers are continuously improving their countermeasures while we try to catch up, it's an ongoing cat-and-mouse game. Please be patient and don't flood our support or forum with requests, we are working on it 24/7 to get it resolved. Thank you.
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
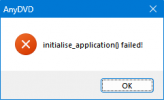
Resolved Weird Windows issue (0xc0000005)
- Thread starter DeepSpace
- Start date
coopervid
Moderator
- Joined
- Mar 15, 2007
- Messages
- 5,194
- Likes
- 2,631
That's like finding a needle in a haystick. You should really re-install. Then install programs you use and create a restore point before each software you install. As a last point before doing that just post what programs are installed on your computer - if you like. Some fishy might be on the list.
cartman0208
Moderator
- Joined
- Apr 3, 2021
- Messages
- 2,344
- Likes
- 2,005
Except the sharing violation I see nothing off here ... and even that might not be a thing...
DeepSpace
Well-Known Member
Thread Starter
- Joined
- Apr 6, 2019
- Messages
- 4,697
- Likes
- 1,871
Already preparing (and planned since the beginning), just posted here in case anyone has an idea. I already thought that it was my fault and I misused the programs or whatever, this post was mainly to find a solution besides a full wipe.You should really re-install.
Thing is, as it also happens on so many other devices and happend on my previous PC as well where I didn't have some of the programs I currently have installed, and even on a guys PC before I even went to install additional programs, it has to be either one tweak program or the fact that I disabled Windows Update before connecting it to the internet, preventing it to load important stuff. Or that I used them wrong, and applied several tweaks and removed things without rebooting in between. So the second program could not see that the previous program has already changed it, but since I did not reboot my PC, it wasn't fully applied. Then I checked the box again in the second program and the setting got messed up.As a last point before doing that just post what programs are installed on your computer - if you like. Some fishy might be on the list.
Issue is, I wiped my fathers PC many months ago, working. I now wiped two laptops during the past months and installed a PC, working (with one laptop barely used). But when I made the guys PC, something went wrong. Since the PC is the same timeframe as the laptops, I used the same programs, but without looking at the screenshots (wherever they are) I can't find it out. Maybe it is even the screenshot program, it is always the first I install to capture everything I do, but then again, why are the other devices working? I have it there as well.
Enough of ranting, I have to prepare for work tomorrow. Sadly.
DeepSpace
Well-Known Member
Thread Starter
- Joined
- Apr 6, 2019
- Messages
- 4,697
- Likes
- 1,871
I don't mind the experience, as long as it has an end. When I find that the future installations all work because I changed how I apply the tweaks or whatever, it is fine and I know how to avoid the issue. But in the previous years it never had an obvious reason on why it suddenly appears, and with the only solution being a full wipe, not even sfc and DISM which are designed for this (I think), I just can't wrap my mind around what the hell is happening. And that is what makes it so frustrating.Boy. Experience can't be tought. But now you have it.
Even though I can't code and the devs don't want to add the eject feature to AnyDVD, I could get my hands on a solution (script) in this forum.
Even though you can't officially uninstall some Windows apps even if they are spam, you can actually do it by using Powershell or programs.
Even though W11 officially doesn't even work on my previous PC, I have it installed on my 10 year old laptop and it runs fine.
And even if you can't officially uninstall or deactivate certain apps on your Android phone, even if they are pure bloatware, you actually can do it with adb. Even if it took me
over 5, maybe 7 years to figure it out (since we had no internet in the beginning), destroying my first two phones over time (and a third) by hassling with root, but eventually I got it to work.
But for four or five years, this issue happens again and again on multiple devices with seemingly no solution and most of all, no apparent reason. Especially since after a wipe, by using the same tweak programs again, it suddenly works fine. And then appears on another PC.
I just think back to my laptop with W7. When W10 came out, I like some changes in the design, but didn't like the OS itself. So I tried to get the changes by using skin packs. Making deep changes into the OS. I am not sure if I once destroyed the system a bit, but I didn't have this issue back then. It started with W10, and I think on my previous PC.
...That had an error of a different kind. The processor (i7 7700) didn't want to get over 0,80 Ghz when booting up. Not sure if it was since the beginning because I still used HDD then and maybe didn't noticed it because of that. You could literally watch the explorer window building. When running for about 20 mins, shutting down and turning it on again, it was on 4,20 Ghz as it should be. When shutting down on the evening and booting up the next day, you guess it, same game. But this was a hardware issue, because even after wiping Windows so the PC could go to someone, it stayed this way. I now had enough and changed motherboard and CPU and now it runs fine. Surprisingly, I didn't have to reinstall Windows even with the different company (AMD instead of Intel) and the PC also never had the 0xc issue after wiping before that change, but I had it when I used the PC before that.
coopervid
Moderator
- Joined
- Mar 15, 2007
- Messages
- 5,194
- Likes
- 2,631
Amen. You still didn't get it. I'm out. You need to change your attitude regarding this. Windows is not a game to play with. It's an animal that always needs to be tamed. So don't open any gaps and if it doesn't behave, roll back to the state when it still behaved. Was my last prayer on this. Amen, again.
DeepSpace
Well-Known Member
Thread Starter
- Joined
- Apr 6, 2019
- Messages
- 4,697
- Likes
- 1,871
I get that you want me to be more careful and make restore points, but if there is more you tried to say, please enlighten me.You still didn't get it. I'm out.
Sure, never change a running system and all that, but if Microsoft is adding crap like Cortana and Edge nobody needs, I have to fix it. I don't want to have 20 apps installed I am never going to use, and things being updated or popping up when I want to do something entirely else.
DeepSpace
Well-Known Member
Thread Starter
- Joined
- Apr 6, 2019
- Messages
- 4,697
- Likes
- 1,871
It is true that I haven't checked for all tweaks if they are doable with Windows itself, should do that. But it appears that at least for some things I still need to use third party apps. For example, not all apps that are preinstalled can be removed using Windows Programs in the settings.Use Windows to disable Windows "features".
Also, not every program is listed in the Task Manager, so I need to use Autoruns. And finally, Windows 11 offers no way to disable the rounded corners, so I need to use Explorer Patcher (not sure if they would disturb me in using Windows, but the screenshot programs can't capture them and always include the background instead of rounding the corner).
Of course you might not care about these things at all. But when something disturbs me, I look for a way to fix it until I found one. I just don't want to accept Microsoft adding things (and other stuff like Androids bloatware) without giving an option to remove or disable it when not needed. Especially when my first (smart)phone only had 2 GB anyway, then I don't need crap preinstalled without an option to get rid of it. But even now when I have enough space, I don't want them to add or change things to "improve" the system. When I want Teams or Cortana, I can go download it. Why is it pre-installed?
DeepSpace
Well-Known Member
Thread Starter
- Joined
- Apr 6, 2019
- Messages
- 4,697
- Likes
- 1,871
As I already mentioned, I think that I misused the programs and did stuff in the wrong order. Not sure if banghead was neccessary, as I only tried to tell you why I believe to need them anyway but already now that i should be more careful.Remember what you here in any airport: "Mind you step"
el Filou
Well-Known Member
- Joined
- Dec 14, 2009
- Messages
- 262
- Likes
- 43
@DeepSpace Did you check the "AppInits" section of Autoruns as suggested by James and others?
When searching the Web for the kind of errors you got, it almost always comes down to either DLLs being corrupted (or sometimes 32-bit DLLs being erroneously loaded by 64-bit programs, e.g. when users manually find DLLs on the Web and manually copy them), or some other application hooking into the processes of every app to do some stealthy stuff.
*a lot* of the people encountering those errors say they went away when disabling a 3rd-party security software.
Edit: also check that there is no weird directory included in the 'PATH' environment variable with shared DLLs in it
When searching the Web for the kind of errors you got, it almost always comes down to either DLLs being corrupted (or sometimes 32-bit DLLs being erroneously loaded by 64-bit programs, e.g. when users manually find DLLs on the Web and manually copy them), or some other application hooking into the processes of every app to do some stealthy stuff.
*a lot* of the people encountering those errors say they went away when disabling a 3rd-party security software.
Edit: also check that there is no weird directory included in the 'PATH' environment variable with shared DLLs in it
Last edited:
.....not even sfc and DISM which are designed for this (I think)....
While SFC and DISM are powerful tools, they aren't guaranteed to fix all system problems. They're specifically designed to handle problems with Windows system files. If a user has made a change to the system that is not specifically related to these system files, SFC and DISM may not be able to resolve the problem.
For example, if a user has deleted a critical system file, SFC can often replace it. Similarly, if a system file has been corrupted, SFC and DISM can often fix it. On the other hand, if the problem is due to a misconfiguration in a software application, or a change in the system settings outside of what SFC and DISM monitor, these tools may not be able to help.
Here are some scenarios where SFC and DISM can be particularly useful:
1. Windows system files are corrupted or have been changed. This can sometimes occur as a result of a virus or malware attack, or an issue with a Windows update.
2. Some Windows features aren't working correctly. Since these features often rely on system files, SFC or DISM can sometimes fix the issue.
3. Windows is experiencing blue screen or other stability issues. These can sometimes be caused by issues with system files.
On the other hand, these tools are less likely to be able to resolve problems such as:
1. Issues with third-party software or drivers. These aren't part of the core Windows system files, so SFC and DISM typically can't fix them.
2. User configuration mistakes outside of system files. If a user has made a change to the system that doesn't involve system files - for example, changing a setting in a software application - SFC and DISM won't be able to undo this.
As for third party tools:
It is often useful to use third-party tools to achieve enhanced functionality or customizations that may not be readily available within the OS itself. However, utilizing these tools can present risks, such as system instability, data loss, and potential security vulnerabilities.
System instability might occur if the modifications made by these tools are incompatible with your current setup, or if they conflict with other settings. Data loss can happen directly (if the modifications involve deleting files) or indirectly (through system instability causing difficulty in accessing your data). As for security vulnerabilities, third-party tools, especially those from unverified sources, might have exploitable weak points or could even contain malicious software.
Given these risks, it's crucial to backup your system before using third-party tools to modify settings. Backups act as a safety net, allowing you to restore your system to its state at the point of backup if anything goes awry.
I would recommend a ln baseline image, which is essentially a snapshot of a fully configured and functional system, can be incredibly useful. This image serves as a 'golden reference point' that you can fall back to whenever needed. It provides several advantages:
1. **Fast Recovery:** If your system encounters a problem, you can use the baseline image to quickly restore it to a known good state, without having to manually reinstall and configure everything.
2. **Consistency:** In a setting where you're managing multiple systems, a baseline image ensures every system starts from the same configuration, making management and troubleshooting much easier.
3. **Testing and Validation:** With a baseline image, you have a controlled environment for testing system changes or new software. You can revert to this baseline after each test, ensuring each test begins with the same system state.
Creating a baseline image for your system is highly recommended, particularly if you have a complex or customized setup. If you ever need to reinstall your operating system or duplicate your setup on another machine, having a baseline image can save you a significant amount of time and effort. Instead of manually reinstalling and reconfiguring everything, you can simply apply the baseline image to return to your desired state.
It's like a "model home" for your computer system – a fully furnished and operational setup that you can replicate whenever needed, making it a valuable resource for system management and recovery.
Kindly note, while I can share insights based on over 30 years of experience in the IT industry, it is ultimately up to each user to decide how they manage and configure their systems. Remember, each system and user requirement is unique, and there's no one-size-fits-all solution. The practices I've described are general recommendations designed to promote system stability and security, but they should be tailored to fit individual needs and contexts.
DeepSpace
Well-Known Member
Thread Starter
- Joined
- Apr 6, 2019
- Messages
- 4,697
- Likes
- 1,871
Thanks tectpro for this detailed explanation. I am not sure if I heard of an baseline image before. But I used NTlite to customize the .iso last year. Maybe it is the term for exactly this process and I just didn't knew it. However, since 22H2, 23H2 are a thing, I thought it might be easier to make a script that applies the changes instead of using different third-party programs, especially when I would need to do it again when a new .iso comes out. I just didn't manage to try that till now, will do so at a later time.
Thanks tectpro for this detailed explanation. I am not sure if I heard of an baseline image before. But I used NTlite to customize the .iso last year. Maybe it is the term for exactly this process and I just didn't knew it. However, since 22H2, 23H2 are a thing, I thought it might be easier to make a script that applies the changes instead of using different third-party programs, especially when I would need to do it again when a new .iso comes out. I just didn't manage to try that till now, will do so at a later time.
I'm glad you found the explanation useful.
A baseline image is similar to what you've created with NTlite - a custom .iso file. You could consider this your own personal baseline, a pre-configured operating system image that includes your desired settings and applications.
However, a key difference might be that a traditional baseline image often refers to a snapshot of a fully deployed and configured system, rather than just an installation media. It can include not only the OS but also installed applications, settings, updates, and more.
Regarding your idea of creating a script to apply changes each time a new .iso comes out, it's indeed a practical approach that could automate the customization process and save time in the long run.
However, there are several things to keep in mind:
1. **Complexity and Maintenance:** Depending on what changes you need to apply, writing such a script could be a complex task. It would require a deep understanding of the Windows OS and the specific changes you wish to make. Plus, you'd need to maintain and update this script as new versions of Windows are released, or as your requirements change.
2. **Potential Risks:** As with third-party tools, scripts have the potential to cause system instability if they change system settings or files in a way that Windows doesn't expect or can't handle. Always test your script in a controlled environment (like a virtual machine) before running it on your main system.
3. **Compatibility with New Releases:** Not all changes you apply to one version of Windows will necessarily work the same way on a future version. Microsoft occasionally makes significant changes to the system architecture, which could affect how your script works.
As for using tools like NTlite, while they provide a user-friendly interface and make the customization process easier, there are also risks:
1. **Potential Risks:** NTlite makes changes to the installation media, which can lead to system instability if not done correctly. Always test your customized .iso in a controlled environment before deploying it on your main system.
2. **Future Compatibility:** As with scripts, the changes you make for one version of Windows might not work for a future version. Always test new .iso files with each Windows release.
3. **Security:** Since you're modifying the installation media, there's a risk of introducing security vulnerabilities if you're not careful. Always ensure you're using a trustworthy source for your original .iso files, and be cautious about any additional software you're including in your custom .iso.
In summary, whether you decide to continue using tools like NTlite, or move towards creating your own scripts, always prioritize testing in a controlled environment before deploying any changes to your main system. And don't forget to keep backups or baseline images for quick recovery if things don't go as planned.